May 22, 20266 min read
IAM systems deserve much more attention – they may work under the hood, but they are the very key to all data and functionality of an online service.
May 19, 20266 min read
Concrete methods and best practices for secure access to data in everyday life.
May 5, 20269 min read
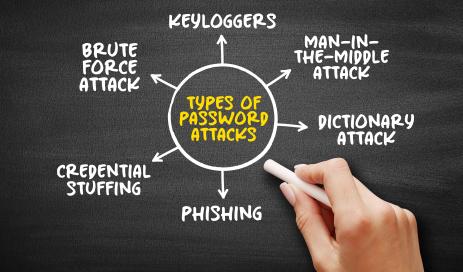
From seconds to practically impossible: How passwords, passphrases and passkeys affect the security of login systems.
Apr 21, 202617 min read
This report highlights the key challenges in data protection and cybersecurity in the first quarter of 2026.
Apr 14, 20269 min read
A modern access system must be equally convincing in the areas of security, ease of administration, easy adaptability to customer needs and user-friendliness.
Mar 26, 20266 min read
Cybercriminals bypass two-factor authentication through manipulation of humans (also known as “social engineering”).
Jan 20, 202619 min read
Join us as we take a look at the most talked-about challenges in data protection and cybersecurity in the fourth quarter of 2025.
Nov 11, 20257 min read
Using cloaking to fake legitimate websites to obtain personal user data through phishing.
Oct 28, 202513 min read
The last part of our hacking series describes how we can best protect ourselves against hacker attacks and how we as users can reduce the risk of attack as much as possible.
Oct 14, 202516 min read
Engity's overview of the most discussed challenges in data protection and cybersecurity in the third quarter of 2025.
Oct 7, 202513 min read
As an open standard, OpenID Connect offers a secure and consistent way to verify user identities across different applications and services.
Sep 30, 202512 min read
A brushing attack is the unsolicited sending and leaving of packages in e-commerce retail.